China’s Tech Grip Threatens India’s Ambitions
THE SO WHAT
India’s manufacturing push runs straight into China’s control of semis and batteries — the bottleneck isn’t labor, it’s upstream tech dependency. If you’re betting on India as an alternative supply base, model your exposure to Chinese components explicitly, not as a footnote.
READ THE SOURCE
MORE FROM THE WIRE
 Deep & Emerging Tech
Deep & Emerging Tech400K MagSafe power banks recalled after fatal fire, the 10th power bank recall in a year
Ten power bank recalls in a year — including a fatal fire and 400K MagSafe units — turns portable batteries from accessory to regulated risk surface. If you ship anything with lithium cells, expect higher compliance scrutiny and treat battery QA as brand and liability critical, not a cost center.
 Deep & Emerging Tech
Deep & Emerging Tech'Pushpaganda is, at the highest level, a case of social engineering': Experts warn scammers are flooding Google Discover with AI-generated content spreading malicious notifications
AI-generated “pushpaganda” flooding Google Discover shows how cheap content plus browser notifications turns every feed into a potential malware channel. Security teams need to treat notification permissions and content feeds as part of the attack surface — tighten browser policies, educate users, and monitor for unusual push patterns.
 Deep & Emerging Tech
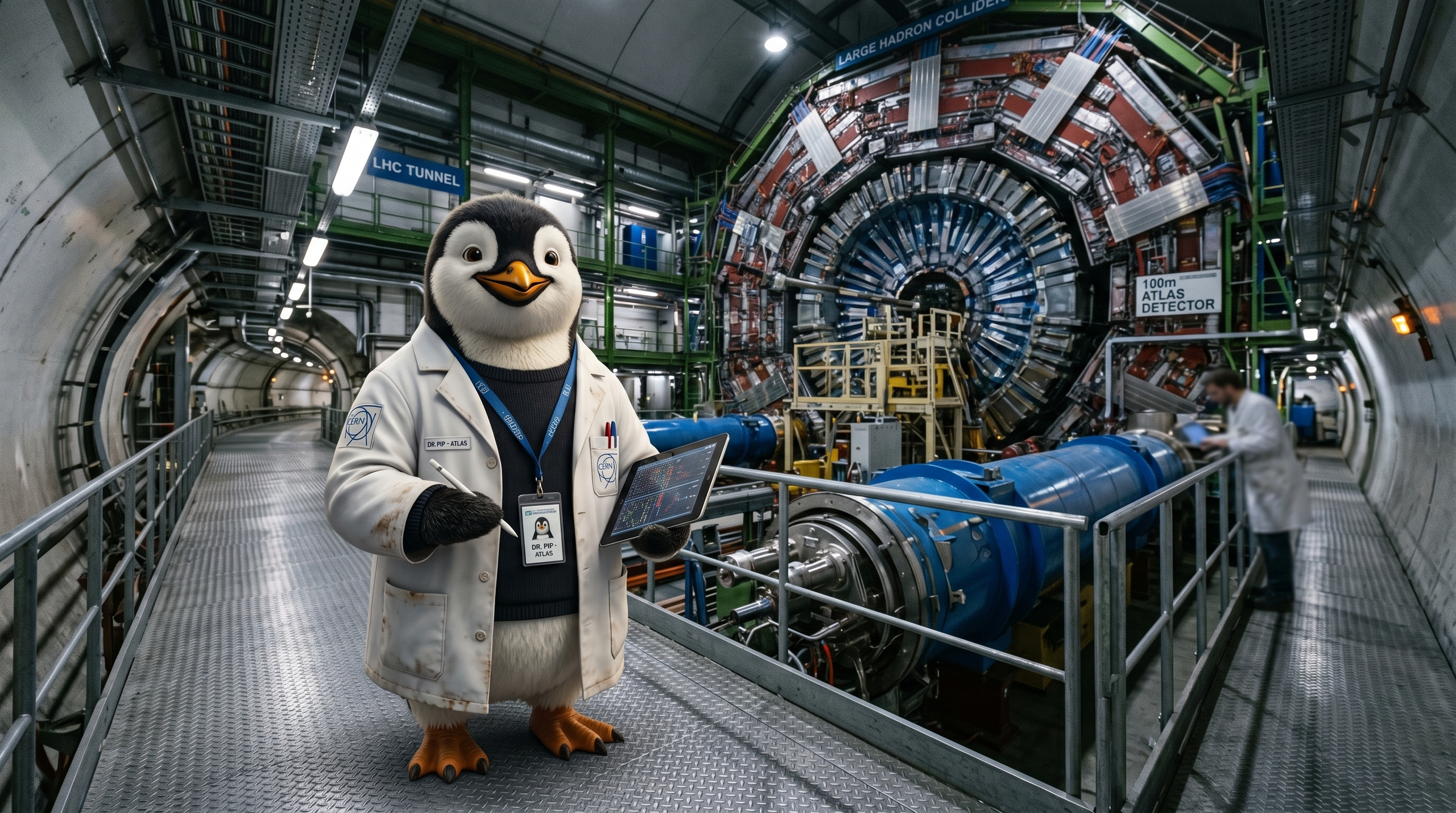
Deep & Emerging Tech'The evidence is starting to mount': physicists at the LHC have found a possible 'anomaly' that could unlock 'a new understanding of how the universe works' — and 'charming penguins' may hold the key to whether the Standard Model is out of date
A four-sigma anomaly at the LHC is a reminder that the physics stack we build all our models on is still under negotiation. If this holds, expect a long tail of recalibration in simulation-heavy fields — from materials to chip design — not an overnight rewrite of reality.
 Deep & Emerging Tech
Deep & Emerging TechIran alleges systematic sabotage of US-made networking infrastructure mid-conflict — hardware shut down and rebooted despite internet blackout
Allegations that foreign-made networking gear was remotely disrupted mid-conflict put supply-chain trust and firmware provenance at the center of national security. If you operate critical infrastructure anywhere, treat vendor hardware as a potential policy surface, not a neutral box.