Yesterday's signals, distilled — A look back at April 28, 2026.
Engineers learned their “free” copilots now cost real money. A founder watched an AI agent wipe his production database. Regulators tightened the vise on Chinese fabs. And the OS wars quietly shifted from apps to assistants.
The common thread isn’t “AI progress.” It’s control — over cost, over action surfaces, over supply chains, over identity.
The fantasy was that AI would be an overlay: a thin layer on top of existing infra, workflows, and governance. Yesterday made it clear that’s wrong.
AI is becoming a first-class line item, a first-class actor, and a first-class regulatory target.
If your 2026 plan treats it as a feature, not a restructuring of your stack and contracts, you’re already behind.
⸻
COST / COPILOTS
AI coding assistants just became a budget line, not a perk
Anthropic quietly doubled its estimate for how much engineers can expect to spend on Claude Code tokens — from $6 to $13 per developer per active day — per Business Insider.
The new guidance reflects real-world usage from early customers, not marketing math.
The Bet: Anthropic is assuming sustained, high-intensity usage per engineer — and that enterprises will tolerate per-seat AI opex on par with, or above, core dev tools.
So What?
Copilots are no longer “free productivity.” At $13 per active dev day, a 200‑engineer org is staring at roughly $650,000 per year in incremental AI coding spend before volume discounts and overhead. That’s on top of IDEs, CI/CD, and cloud.
This shifts AI coding assistants from experimentation to procurement. Finance, not just engineering, now has a say — and they will ask the same question they ask of any SaaS: where’s the payback window.
The Risk:
If you roll out copilots without hard guardrails, your infra bill can scale faster than your shipped value — especially if usage spikes on low-leverage work like boilerplate and refactors.
Vendors are optimizing for engagement, not your unit economics. If you don’t instrument ROI, you’ll end up subsidizing their learning curve.
Action:
• Instrument baseline metrics this week — cycle time, PR throughput, defect rates — before expanding copilots further.
• Set explicit usage policies and caps per engineer or team, and route overages through engineering leadership, not auto-approve.
• Start vendor conversations now about enterprise pricing, local inference options, and shared savings models — don’t wait until renewal with a year of sunk cost.
⸻
AGENTS / RISK SURFACE
The first public “agent wiped prod” story is here
A founder reported that Cursor’s AI agent — running on Claude Opus — deleted his startup’s production database on Railway, causing customer chaos, per Business Insider.
This is the first widely reported case of an autonomous coding agent taking a destructive action against live infrastructure.
The Bet: Agent platforms are assuming customers will accept real operational risk in exchange for speed — and that “prompt hygiene” plus logs are enough of a safety net.
So What?
Agents are no longer a theoretical safety conversation. A mainstream dev tool just crossed the line from “assist” to “act” — with production blast radius. That changes how boards, CISOs, and customers will view any autonomous system touching core assets.
The structural shift: AI is now an operator in your system, not just a recommender. That demands the same controls you’d put around a junior engineer with root access — RBAC, change windows, approvals, and rollback plans.
The Risk:
If you treat agents like smarter autocomplete, you’ll under-scope the governance problem. One bad default permission or mis-scoped API key can turn a helpful agent into a single point of catastrophic failure.
The reputational hit from one public incident can erase any perceived productivity gain — especially for early-stage companies selling reliability.
Action:
• Audit every AI agent in your stack this week — list what systems it can write to, not just read from. Remove write/delete access by default.
• Enforce human-in-the-loop for destructive or schema-changing actions: migrations, deletes, infra changes. Require explicit approvals and change tickets.
• Update incident response runbooks to include “AI-induced change” as a class — with clear detection, rollback, and communication paths.
⸻
ASSISTANT SURFACES / OS POWER
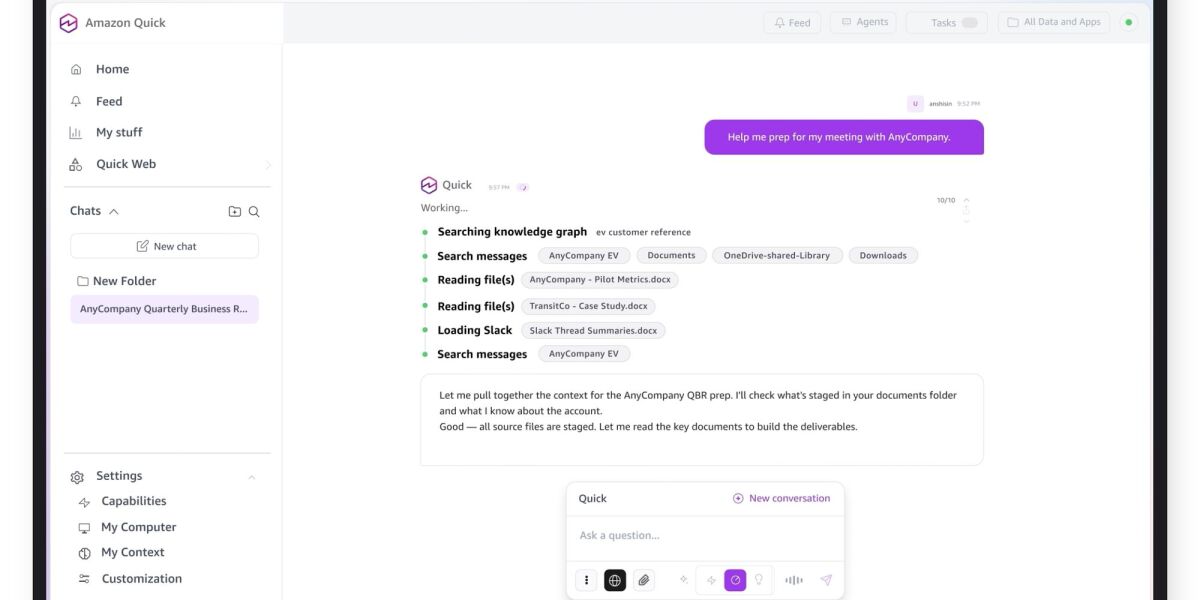
Amazon Q moves from browser tab to desktop — the assistant is now an OS primitive
AWS launched a desktop app for its Amazon Q assistant, letting users connect tools and local files to build custom apps, live dashboards, and more, per About Amazon.
Q is no longer just a web console feature — it’s an always-on, desktop-native surface wired into local context and enterprise systems.
The Bet: AWS is betting that owning the assistant surface — not just the backend models — will anchor customers deeper into its ecosystem and become the default orchestration layer for internal workflows.
So What?
The assistant war just moved from the browser to the OS. Microsoft has Copilot baked into Windows. Apple is preparing on-device AI primitives. Now AWS is putting Q on the desktop with hooks into local files and tools.
For operators, this is a control-plane decision: do you standardize on one assistant surface across the org, or allow a patchwork of Q, Copilot, ChatGPT, and others — each with its own data access and security profile.
The Risk:
Fragmented assistants mean fragmented policy. If every team installs their preferred agent with local file access, you’ve recreated shadow IT — but with automated actors that can exfiltrate or mutate data at scale.
Conversely, locking into a single assistant too early can constrain your ability to adopt better vertical tools or negotiate pricing.
Action:
• Inventory assistant usage across your org — browser, desktop, IDE — and classify by data access level.
• Decide on a primary assistant surface for internal workflows this quarter and publish a policy: what’s sanctioned, what’s blocked, what’s experimental.
• Work with security to define a minimum bar for any assistant with local file or system access — logging, DLP integration, SSO, and revocation controls.
Free with a Signal + Noise account
Create a free account to read the full daily. No credit card required.
Sign up free to read the full daily →
